
BLOG
What is a Security Risk Assessment? A CISO’s Guide for Ensuring Board-Worthy Outcomes
Published On March 26, 2026
by Morgan Hague
Redefining the Security Risk Assessment for the Boardroom
As a CISO, you are familiar with Security Risk Assessments (SRAs). How can you position the strategic value and mandatory nature of an SRA to your organization’s executive leadership?
If you are a CISO in the healthcare sector today, you don’t need a blog post defining the elementary concepts of cyber risk. You live it every day. You know that the threat landscape is volatile, that ransomware groups are aggressively targeting healthcare organizations, and that your attack surface expands with every new IoT device connected to the network.
The challenge lies in articulating the necessity of an SRA and justifying the cost to a board of directors balancing razor-thin operating margins. When the board asks, “Why are we spending six figures on a consultant to tell us what we already know are problems?” you need a robust answer that goes beyond technical jargon.
This article reframes the SRA as a strategic instrument that protects patient safety, strengthens financial resilience, and ensures regulatory compliance.
Producing a Strategic Diagnostic
For clarity when speaking to non-technical stakeholders, let’s strip away the nuance. At its core, an SRA is an accurate and thorough evaluation of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of all electronic protected health information (ePHI) your organization creates, receives, maintains, or transmits.
The SRA is a holistic diagnostic that looks at technology, people, and processes. An SRA identifies where ePHI could potentially leak or be held hostage:
- Where do you store ePHI?
- Who can access ePHI?
- How do you protect ePHI?
- What vulnerabilities affect ePHI?
The presence of a “clean” SRA doesn’t mean your organization is “safe” for a year. The SRA is simply a point-in-time baseline to use as justification for an investment in solutions that provide continuous monitoring and visibility.
For the CISO, the SRA is the baseline map. You cannot build a defensible security strategy if you do not know the terrain.
The “Stick”: The HIPAA Regulatory Mandate & Compliance Conditions
When justifying an SRA to executive leadership, the first stop must always be regulatory obligation. In healthcare, this is not optional.
The Health Insurance Portability and Accountability Act (HIPAA) Security Rule is explicit. Under the Administrative Safeguards standard, specifically 45 CFR § 164.308(a)(1)(ii)(A), covered entities and business associates are required to:
“Conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information held by the covered entity or business associate.”
Furthermore, this isn't a “one-and-done” activity. The Rule requires organizations to implement security measures sufficient to reduce risks to a reasonable and appropriate level and to periodically review the effectiveness of those measures.
The lack of a current SRA is one of the most commonly cited HIPAA violations and can lead to:
- OCR penalties.
- Mandated correct action plans.
- Reputational harm.
- Increased cyber insurance rates.
The Boardroom Translation: If the Office for Civil Rights (OCR) comes knocking on our door requesting an audit, especially following a breach, the very first document they will ask for is our most recent SRA. Failure to produce a current, thorough SRA is often cited in resolution agreements and can significantly increase financial penalties. The SRA is the foundation upon which all other HIPAA Security compliance is built.
While HIPAA provides the legal “stick”, other industry frameworks create operational requirements that make an SRA indispensable:
- SOC 2 (AICPA’s Trust Service Criteria): Achieving SOC 2 compliance requires organizations to demonstrate a structured approach to identifying and managing security risks. Performing an SRA is a foundational activity for meeting the “Risk Assessment” and “Control Monitoring” criteria within the Security and Availability categories.
- HITRUST CSF: HITRUST incorporates multiple authoritative sources, including HIPAA, NIST, and ISO, and requires a comprehensive, documented risk analysis as part of the control maturity model. An SRA is essential to achieving, maintaining, and renewing HITRUST certification.
- CMS Promoting Interoperability Program: To meet CMS requirements, eligible hospitals and critical access hospitals must conduct or review a security risk analysis annually and address identified risks to the protection of ePHI. Completion of an SRA is required to attest to program compliance.
Failing to meet these requirements can lead to:
- Loss of Business: Many partners and payers now require HITRUST or SOC 2 reports as a condition of doing business.
- Financial Impact: Failing CMS requirements directly affects reimbursement rates.
- Market Credibility: These frameworks prove to the market that your organization is a safe steward of data.
Together these frameworks and programs reinforce the SRA as a practical necessity for organizations that rely on industry certifications, federal program participation, or partner assurances even when not strictly mandated by law.
The “Carrot”: The Strategic Purpose of an SRA
While compliance is the baseline, it should not be the only argument. Positioning an SRA solely as a compliance hoop minimizes your role as a strategic business leader.
To justify the resources required for a comprehensive assessment (especially one conducted by an objective third party), focus on the following strategic purposes.
1. Defensible Budgeting
Boards love data. They hate abstract requests for money. An SRA provides the empirical evidence needed to prioritize your budget. Instead of saying, “We need more money for firewalls,” an SRA allows you to say, “Our assessment identified a high risk in our legacy billing application that could cost us $X per day in downtime. Here is the investment required to mitigate that specific business risk.”
2. Operational Resilience and Patient Safety
In healthcare, cyber risk is patient safety risk. If an SRA identifies a weakness in the network segmentation of biomedical devices, that is not an IT problem; it is a clinical operations problem. If the network goes down, we don’t just lose data, we lose the ability to provide patient care. The purpose of the SRA is to ensure that digital systems remain available so that clinicians can deliver care without interruption.
For example, during our most recent SRA, we found a misconfigured biomedical VLAN that could have allowed attackers to disrupt infusion pumps, posing direct patient safety risk.
3. Mergers and Acquisitions (M&A) Due Diligence
Healthcare continues to consolidate rapidly. If your organization is looking to acquire a clinic or merge with another hospital system, you are inheriting their digital toxic waste. A pre-M&A SRA is crucial for understanding the true “cost” of an acquisition, factoring in the remediation required to bring the new entity up to your security standards.
4. Cyber Insurance Eligibility
Cyber insurance premiums are skyrocketing, and carriers are demanding proof of mature security controls. A recent, thorough SRA is increasingly becoming a prerequisite just to get a quote, let alone bind a policy with reasonable coverage limits.
Presenting Findings Effectively
The fastest way to lose funding for future SRAs is to drop a 300-page technical report filled with CVE scores onto the board table.
The purpose of the SRA is to drive action. When presenting annual results to leadership:
- Lead with Visuals: Use heat maps or similar (e.g., red = bad) based on business impact, not technical severity.
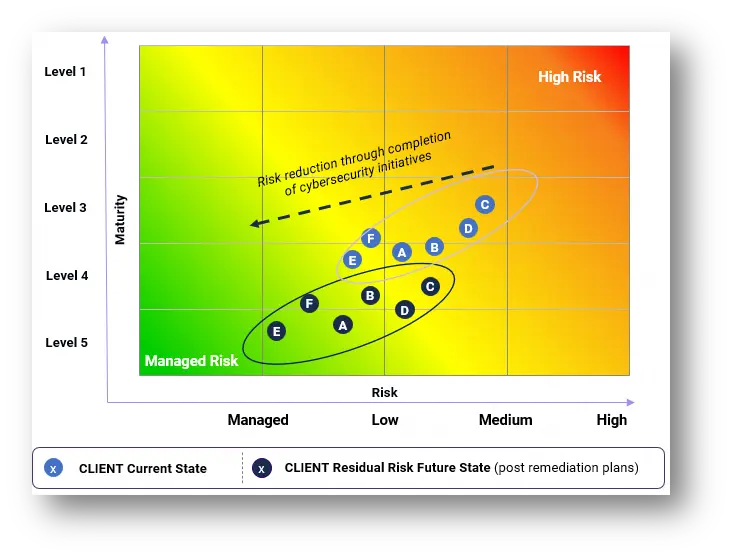
- Monetize the Risk: Wherever possible, translate technical gaps into potential financial loss (e.g., regulatory fines, operational downtime revenue loss, breach response costs).
- Provide a Remediation Roadmap: Don’t just present problems. Present a prioritized plan of action with estimated timelines and resource requirements.
- Align SRA outcomes with your organization’s strategic goals:
- The Billing system’s legacy operating system presents a potential for $X/day in downtime due to system failure.
- Unsegmented VLANs present a direct risk to life-saving devices like infusion pumps.
- An incomplete inventory of ePHI presents an increased risk of the OCR assessing multi-million penalties.
- Lack of a recent SRA could create an inability to renew or to bind our cyber insurance policies.
Conclusion
As a CISO, you know that an annual SRA is the cornerstone of a mature information security program. An SRA is required by HIPAA, demanded by the threat landscape, and essential for operational resilience.
Your job is to ensure your board understands that an SRA is not a sunk cost to satisfy a regulator. An SRA is a strategic investment in the organization's ability to continue delivering patient care safely in a digital world.
Partnering for Board‑Level Confidence
Conducting a Security Risk Assessment (SRA) that satisfies both the HIPAA Security Rule and a discerning Board of Directors is no small feat. It requires more than technical scanning; it calls for a deep understanding of healthcare clinical workflows and the ability to translate complex vulnerabilities into clear, business‑aligned risk insights.
This is where Meditology’s experience comes into play.
As a healthcare‑focused cybersecurity and risk management firm, Meditology helps CISOs navigate the complexities of HIPAA compliance while producing the strategic artifacts needed to support board‑level discussions. Rather than delivering a static list of “high‑risk” findings, we provide a defensible, prioritized roadmap that aligns security risk with organizational resilience and patient safety.
An effective SRA should be more than a compliance exercise. When approached strategically, it becomes a tool for informed decision‑making, executive confidence, and long‑term risk management.
If you’d like to discuss how your next SRA can better support both regulatory expectations and leadership priorities, Meditology is available to help.
About the Author
Morgan Hague | Sr. Manager, IT Risk Management & AI Security Lead
Morgan is an experienced security and emerging technologies consultant, with varied expertise across information security, organizational governance, and IT audit practices. As the leader of the Security Risk Assessment and Strategic Risk Transformation service lines at Meditology, he has led and contributed to hundreds of consulting engagements across public and private entities.
Since 2019, he has served as lead architect and product owner of an innovative risk quantification, analysis, and reporting solution utilizing MITRE ATT&CK and similar authoritative sources to establish a data-driven and dynamic mechanism to assess, report on, and manage organizational risk – supporting a variety of premier healthcare organizations, including the nation’s largest hospital system. Morgan is currently the President of InfraGard Atlanta, and an effort lead for OWASP’s AI Security Guide.